What hiring managers actually look for
Security hiring managers are among the most technically rigorous in IT. They scan for three things before reading further:
-
1
Industry-recognized certifications. CompTIA Security+, CEH, CISSP, OSCPcertifications are the gatekeeping mechanism in security. If the posting lists a specific cert and you don't have it, your resume often doesn't make it past the ATS.
-
2
Hands-on tool experience. SIEM platforms (Splunk, QRadar, Sentinel), EDR tools (CrowdStrike, Carbon Black), vulnerability scanners (Nessus, Qualys), and forensic tools (Wireshark, Volatility). Listing these by name matters.
-
3
Incident response and threat detection experience. Have you triaged alerts, investigated incidents, or written detection rules? Security is an operational field. Managers want to see that you've handled real events, not just studied theory.
If your resume communicates these things in the first 7-second scan, you'll make it to the detailed read. Everything below is about making that happen.
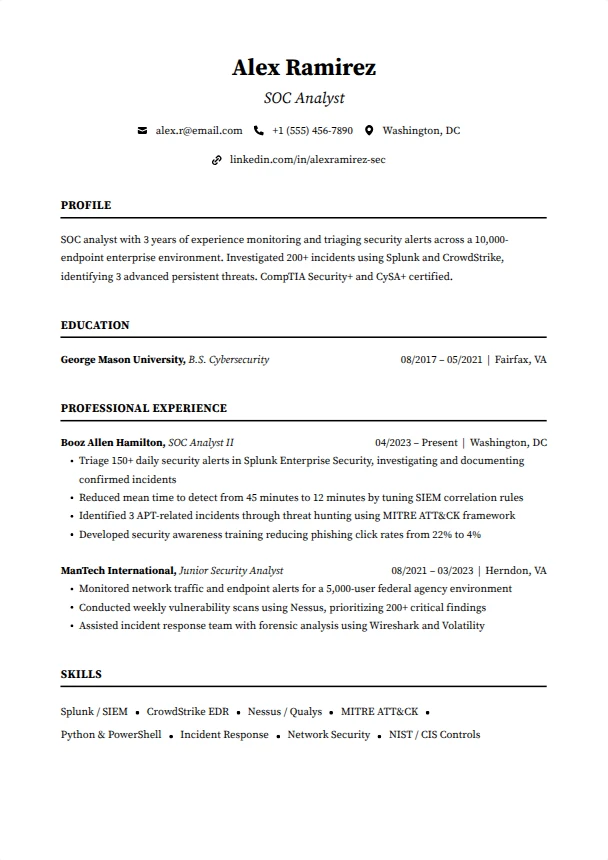
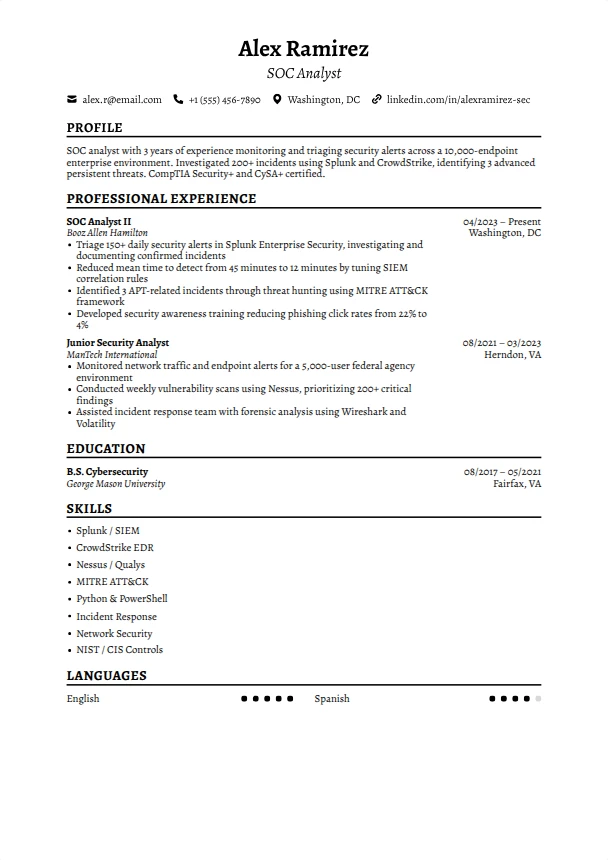
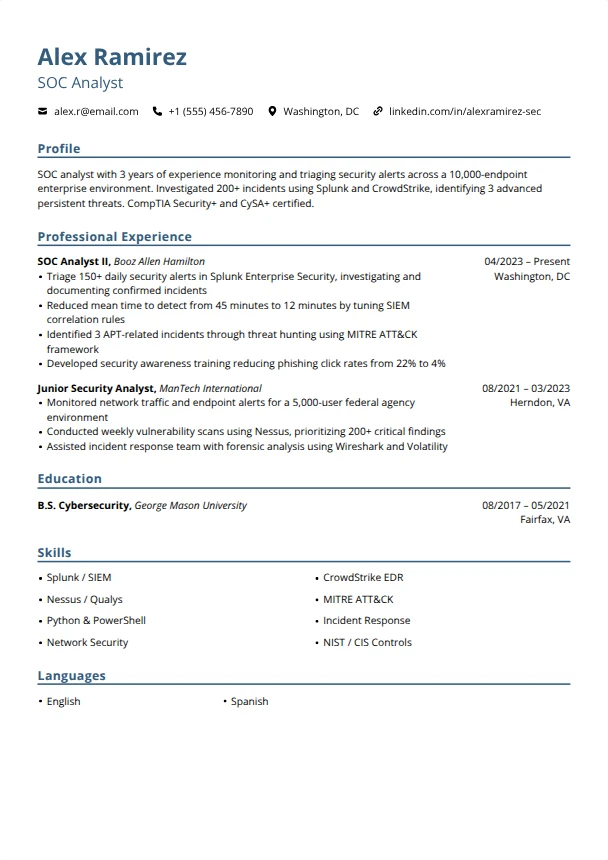
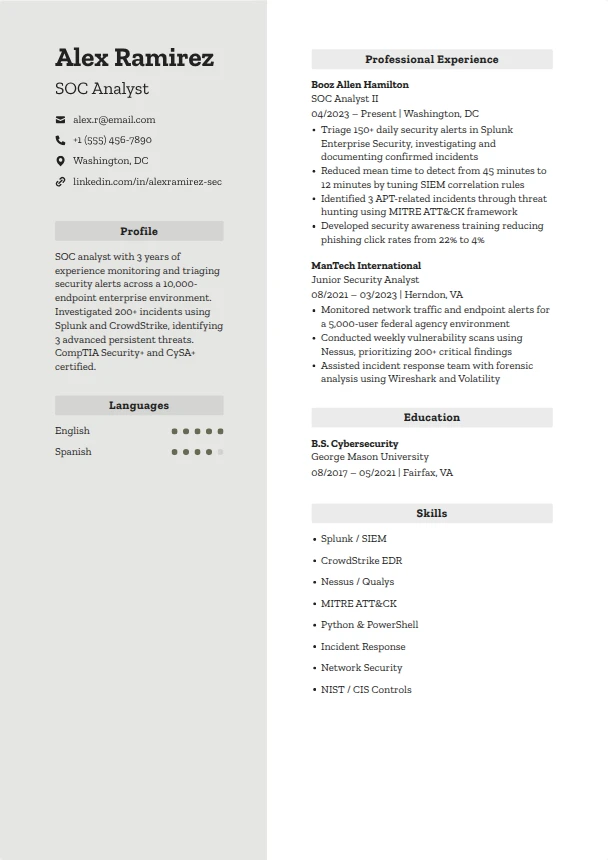
How to structure your resume, section by section
The order matters. Here's what a strong cybersecurity resume looks like from top to bottom:
1. Contact header
Name, email, phone, location (city + state), and LinkedIn. If you have a security blog, CTF profile (HackTheBox, TryHackMe), or GitHub with security tools, include those links.
Alex Ramirez · [email protected] · (555) 456-7890 · Washington, DC
linkedin.com/in/alexramirez-sec · hackthebox.com/profile/alexr
2. Professional summary (2-3 sentences)
Lead with your security specialization, years of experience, top certification, and a quantified achievement. Security managers want to know immediately whether you're SOC, GRC, pentest, or engineering focused.
Strong: "SOC analyst with 3 years of experience monitoring and triaging security alerts across a 10,000-endpoint enterprise environment. Investigated 200+ incidents using Splunk and CrowdStrike, identifying 3 advanced persistent threats. CompTIA Security+ and Cy SA+ certified."
3. Certifications
Security certifications are non-negotiable for most roles. List them prominently. Order by relevance to the target role, not chronologically.
CompTIA Security+ (2024) · CompTIA Cy SA+ (2025) · CEH (2025) · OSCP (in progress)
4. Technical skills
Group by domain: SIEM & Monitoring, Endpoint Security, Vulnerability Management, Networking, Scripting. Security resumes need more specific tool names than general IT resumes.
SIEM: Splunk, Microsoft Sentinel, QRadar
Endpoint: CrowdStrike Falcon, SentinelOne, Carbon Black
Vuln Mgmt: Nessus, Qualys, Rapid7 InsightVM
Scripting: Python, PowerShell, Bash
Frameworks: NIST CSF, MITRE ATT&CK, CIS Controls
5. Work experience
Focus on incidents handled, alerts triaged, vulnerabilities remediated, and policies implemented. Use specific numbers: endpoint count, alert volume, response times, compliance scores.
Strong: "Triaged 150+ daily security alerts in Splunk, escalating 12 confirmed incidents over 6 months. Reduced mean time to detect from 45 minutes to 12 minutes by tuning SIEM correlation rules and reducing false positives by 60%."
6. Education & security clearance
Degree, school, graduation year. If you hold or are eligible for a security clearance (Secret, Top Secret, TS/SCI), include itthis is a major differentiator for government and defense roles.
Key skills to include
These are the most in-demand skills across cybersecurity job postings in 2026. Tailor your list to match the specific role SOC analyst, security engineer, and GRC analyst need different emphasis.
Tip: If the posting mentions a specific SIEM or EDR tool, use their exact product name. ' Experience with Splunk Enterprise Security'matches differently than just ' SIEM experience'in ATS.
Resume summary examples you can steal
Use one as a starting point, then swap in your own technologies, numbers, and achievements.
"CompTIA Security+ certified cybersecurity professional with hands-on experience from a 6-month SOC internship. Monitored security alerts in Splunk, investigated phishing campaigns, and assisted with incident documentation for a 5,000-endpoint environment. Active HackTheBox and TryHackMe participant with 50+ completed challenges."
Why it works: Certification, real SOC experience, specific tools, demonstrates continuous learning.
"Security engineer with 4 years of experience designing and implementing security controls for cloud and on-premises environments. Deployed CrowdStrike across 8,000 endpoints, reducing malware incidents by 75%. Built automated vulnerability scanning pipeline using Nessus and Python, cutting remediation time by 40%. Cy SA+ and AWS Security Specialty certified."
Why it works: Deployment scale, measurable reduction in incidents, automation, relevant certifications.
"Senior security architect with 10+ years of experience designing zero-trust architectures for Fortune 500 companies. Led security transformation for a $500M cloud migration, implementing IAM, encryption, and network segmentation across AWS and Azure. Managed a team of 6 security engineers. CISSP and CCSP certified."
Why it works: Enterprise scale, strategic leadership, multi-cloud, executive-level certifications.
"IT systems administrator transitioning to cybersecurity with CompTIA Security+ certification and hands-on experience in vulnerability scanning and incident response. Built a home security lab with Splunk, Suricata IDS, and Kali Linux. Brings 5 years of infrastructure experience including firewall management, patch deployment, and access control directly applicable to security operations."
Why it works: IT background positioned as security-relevant, home lab proves commitment, transferable skills clearly stated.
Writing strong experience bullets
Every bullet point should answer: "What did you do, and why did it matter?" Use this formula:
Before and after examples:
Monitored security events and managed incidents.
Triaged 150+ daily alerts in Splunk Enterprise Security, investigating and documenting 12 confirmed incidents over 6 months, including 3 APT-related events escalated to the CISO.
Performed vulnerability scans and reported findings.
Conducted weekly vulnerability scans across 5,000 assets using Nessus, prioritizing 200+ critical findings and driving remediation SLA compliance from 65% to 92% within one quarter.
Helped improve security policies and awareness.
Developed and delivered monthly security awareness training to 800+ employees, reducing successful phishing simulation click rates from 22% to 4% over 12 months.
Strong action verbs for cybersecurity resumes:
Triaged · Investigated · Detected · Remediated · Deployed · Hardened · Automated · Monitored · Analyzed · Escalated · Assessed · Configured · Documented · Implemented · Scanned · Responded · Contained · Hunted
7 mistakes that get cybersecurity resumes rejected
Listing certifications you haven't earned yet without clarifying
Writing ' CISSP'when you're still studying is dishonest and will cost you the job if discovered. Always add '(in progress)' or '(expected July 2026)' for certs you haven't passed yet.
Using vague phrases like ' monitored security events'
Every SOC analyst monitors events that's the job description. What tool did you use? How many alerts per day? What did you find? Specifics separate you from every other candidate.
Omitting framework knowledge
MITRE ATT&CK, NIST CSF, CIS Controls, OWASP Top 10security managers expect you to know at least one framework. If you've used it in your work, mention it by name.
Not mentioning clearance eligibility
For government and defense roles, clearance status is often the first filter. If you hold a clearance or are eligible for one (US citizen, clean background), say so on your resume.
Overloading with theoretical knowledge
Listing ' knowledge of network protocols'without showing you've used Wireshark to analyze packets doesn't help. Always pair knowledge claims with tool names and practical examples.
Using a flashy resume template
Security professionals should know that ATS systems parse text, not graphics. A clean single-column layout with clear section headers signals that you understand how hiring technology works.
Forgetting to mention scripting
Python, PowerShell, and Bash automation skills are increasingly expected in security roles. If you've written detection rules, automated scans, or built tools, feature it prominently.
What to do if you have no professional experience
Breaking into cybersecurity without professional experience is challenging but doable. Here's how to build a competitive resume:
Get Security+ certified
CompTIA Security+ is the minimum entry point for most cybersecurity roles. It's Do D 8570 compliant, which also makes you eligible for government security positions. This is step one.
Build a home security lab
Set up Splunk (free tier), install Suricata or Snort as an IDS, practice with Kali Linux and Metasploitable. Document your setup and findings. This demonstrates genuine hands-on capability.
Complete CTF challenges and document them
HackTheBox, TryHackMe, PicoCTF, and OverTheWire all provide structured challenges. Rank up, write walkthroughs, and link to your profile. Security managers value candidates who practice continuously.
Leverage IT support experience
If you've worked help desk, you already understand Active Directory, networking, and user management. Frame your IT experience through a security lens: access control, patch management, incident escalation. These are core security functions.
Frequently asked questions
What certifications should I get first for cybersecurity?
Start with CompTIA Security+it's the most widely recognized entry-level security cert and required for many government positions. From there, choose based on your target role: Cy SA+ for SOC/analyst, CEH or OSCP for penetration testing, CISSP for management-track (requires 5 years experience).
How long should a cybersecurity resume be?
One page for under 8 years of experience. Two pages for senior roles, especially if you have multiple certifications, clearance information, and significant incident response history. Every line should earn its place.
Should I include my HackTheBox or TryHackMe profile?
Yes, especially if you're early-career. Link to your profile and mention your rank or number of completed challenges. Security managers view active CTF participation as evidence of genuine passion and practical skill development.
Do I need a CS degree for cybersecurity?
Not always. Many security professionals come from IT support, networking, or military backgrounds. Certifications (Security+, CISSP, OSCP) plus hands-on experience can substitute for a degree in most roles. That said, a degree helps for competitive positions at large enterprises.
Should I mention security clearance on my resume?
Absolutely. If you hold an active clearance (Secret, Top Secret, TS/SCI), put it near the top of your resume it's one of the strongest differentiators in cybersecurity hiring, especially for government and defense sector roles. If you're eligible but don't hold one, say ' Clearance eligible.'
Build your cybersecurity resume now
Pick an ATS-friendly template, add your certifications and security experience, and download a polished PDF in minutes. Free, no account required.
Start Building, It's FreeRelated resume guides
General IT resume for sysadmin, infrastructure, and networking roles.
Full-stack, backend, and frontend engineering roles with code-focused bullets.
SQL, Python, dashboards, and data storytelling for business stakeholders.
HTML, CSS, JavaScript, responsive design, and portfolio presentation.
More resume examples: